Our full featured and customizable visitor management software is hosted on secure cloud servers. Cloud security at SafePass is the highest priority. SafePass customers benefit from data center and network architecture built to meet the requirements of the most security-sensitive organizations.
Features
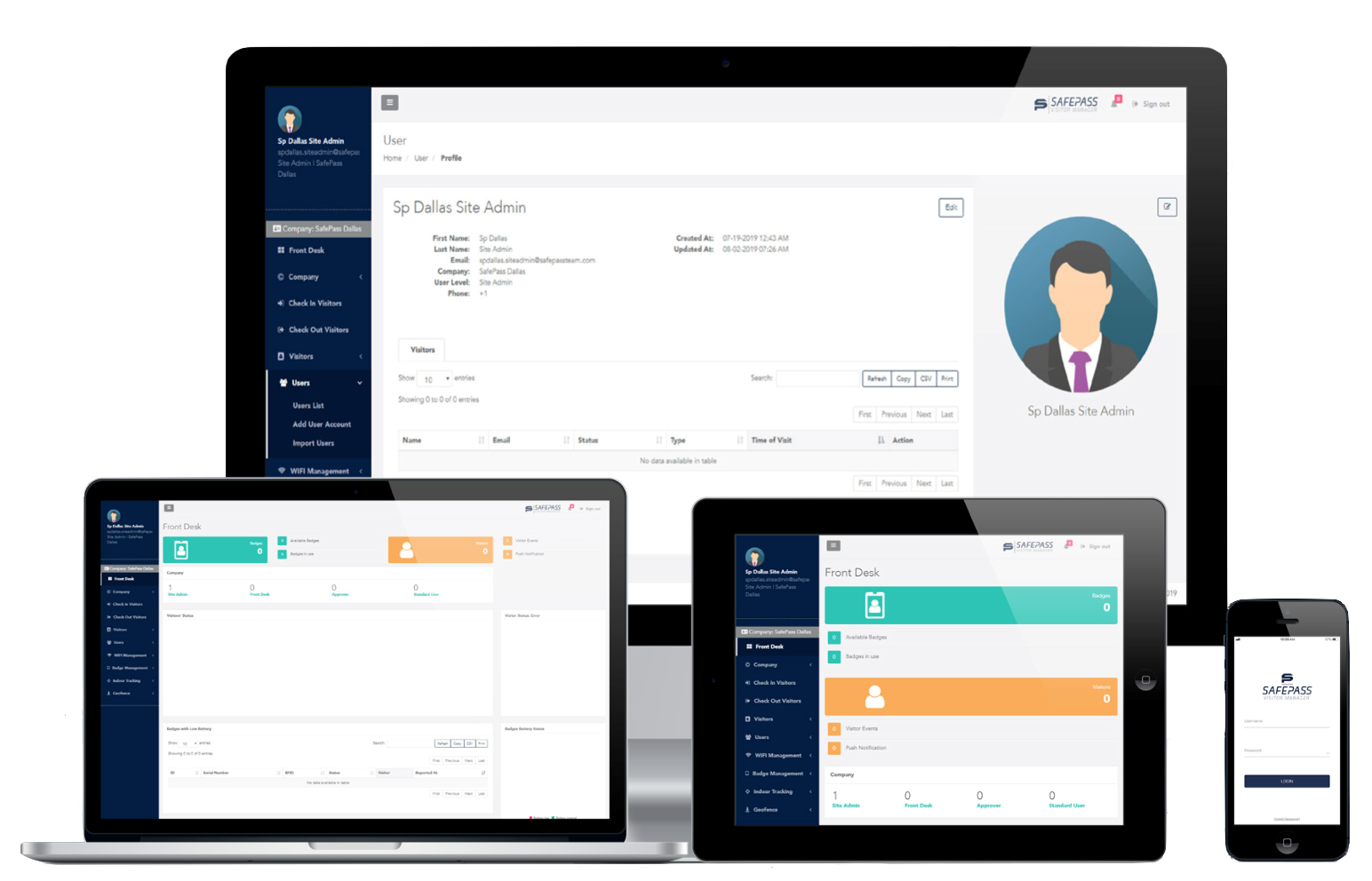
Web-based/Multi-platform Accessible
SafePass Visitor Manager is web-based and can be accessed on any internet capable smart devices from anywhere in the world. No complicated software installation and easily scalable to for multi-location setups.
Facial Recognition
SafePass streamlines the check-in process via facial recognition. The use of an Apple® iPad app simplifies the check-in process. Once a person has been verified, visitors can quickly sign-in, notify the host, and pick up a digital badge for their visit.
Secure Authenticating ID Scanner
Because verifying an ID consistently, quickly and accurately is a must for ensuring security in any environment, the SafePass ID Scanner uses the latest and greatest in ID authenticating technology.
SafePass Wearable Technology Badges
Our unique badges unlock powerful capabilities in the SafePass Visitor Manager software. With features such as real-time location tracking, heat mapping and geofencing, our SafePass Visitor Management System is shaping the future in visitor management softwares.
Historical Transaction Records
Visitor activities are stored on secured cloud servers. Tracking logs are tamper-proof and assures the integrity of your stored records.
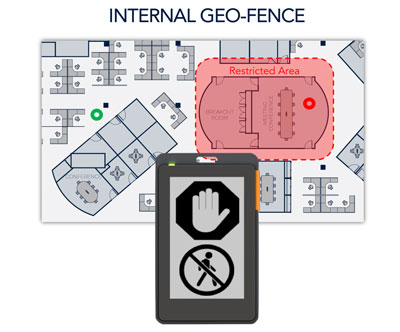
Virtual Geo-Fence
Geofencing establishes virtual boundaries (fencing) around a specific location (geo) to trigger an action as soon as someone enters or leaves the target location. The SafePass Visitor Management System effectively provides geofencing capabilities when used with our digital visitor badges. Some benefits of geofencing includes:
- Theft prevention and asset control
- Prevent unauthorized access of restrictive/sensitive area
- Location base marketing and information
- Better allocation of resources